Security Advisory: Unauthenticated Remote Command Execution in Multiple WAGO Productsdate: May 17, 2023
author: ONEKEY and CERTAINITY joint research team
Introduction
As we already demonstrated through our recent advisories (Asus M25 NAS, Phoenix Contact, NetModule , Festo) ONEKEY's "zero day identification" module is quite versatile when it comes to finding bugs in PHP, Lua, or Python code we find in firmware uploaded to ONEKEY's platform. However, we recently discovered that we were missing an interesting source for PHP taint analysis: PHP wrappers.
PHP comes with many built-in wrappers for various URL-style protocols for use with the filesystem functions such as fopen(), copy(), file_exists() and filesize(). They are sometimes used to read the content of HTTP requests or command line arguments by using php://input, php://stdin, or php://fd/0 (ok the last one is a bit far-fetched and came up when we discussed potential sources for the taint analysis, but you get the point :) ).
We recently added these wrappers as a source and scanned some sample firmware images. Within the scan results was an unauthenticated command injection affecting the web interface of WAGO Series PFC100.
We immediately confirmed our findings on a real device (we got one since the latest advisory) and reported the issue to WAGO. They were extremely fast in responding and fixing the vulnerability (around 45 days from reporting to patch release). Hats off to them and CERT@VDE.
Unauthenticated Remote Command Execution
Affected vendor & product |
|
Vendor Advisory | |
Vulnerable version | Firmware versions >= 16 and <= 23. |
Fixed version | Affected users users must install FW22 Patch 1 or FW24 depending on the affected device. Refer to vendor advisory for more information. |
CVE IDs | |
Impact (CVSS) | 9.8 (critical) (AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H) |
Credit | Q.
Kaiser, ONEKEY Research Lab |
Summary
The “legal information” plugin of the WAGO web-based management interface contains a command injection vulnerability allowing for the execution of arbitrary commands with privileges of the user www.
Impact
A successful exploit allows an attacker to create new users and change the device configuration, which can result in unintended behavior, denial of service, and full system compromise.
Description
The WAGO web admin interface has a "legal information" feature where users can list open source licenses of third party software used by WAGO. This is required to comply with those software licenses.
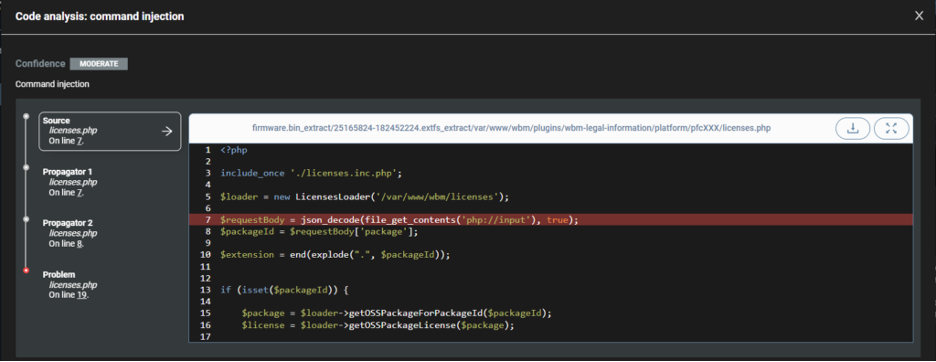
The vulnerability is present in PHP code located at /var/www/wbm/plugins/wbm-legal-information/platform/pfcXXX/licenses.php.
Below we see that a $packageId variable is read from the JSON structure received in the HTTP body through the use of the PHP wrapper php://input.
Next, on line 19, the $packageId variable is used in a shell_exec call without prior sanitization, leading to unauthenticated arbitrary command injection.
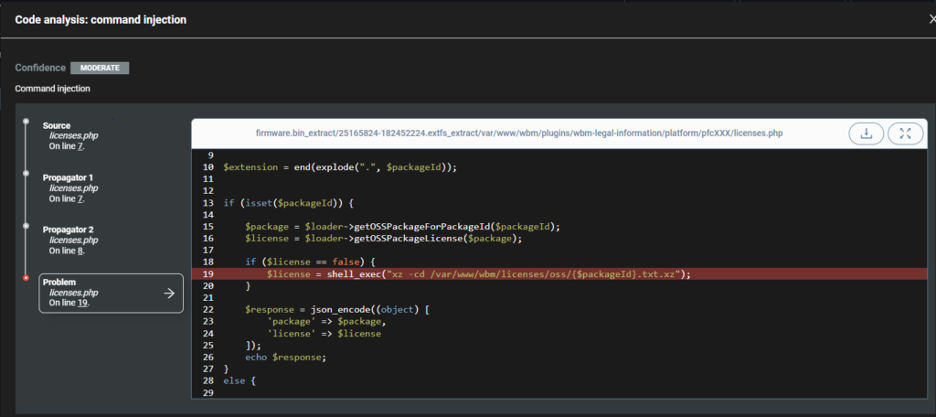
By sending the request below, an attacker would make the device execute the command id:
curl -s -k -X POST --data '{"package":";id;#"}'https://ip.of.device/wbm/plugins/wbm-legal-information/platform/pfcXXX/licenses.php | jq { "package": { "id": ";id;#", "name": ";id;#", "version": null }, "license": "uid=1000(www) gid=1000(www)\n" }
Key Takeaways
This vulnerability serves as an example that static analysis tools needs constant care so as not to miss potential issues. Together with ONEKEY strive to continuously improve our zero-day identification module by identifying what we are potentially missing both in bug classes, and in ways that these can be exploited.
It's also interesting to note that the vulnerability affects a rather uninteresting feature of the product that rather looks static when you don't have access to the code. I know it would not have been my prime focus as a pentester.
Timeline
2023-03-29 – Sent coordinated disclosure request to psirt@wago.com
2023-03-29 – Answer from WAGO PSIRT (Product Security Incident Response Team), establishment of secure communication channel.
2023-03-30 – WAGO PSIRT provides us with CVE (Common Vulnerabilities and Exposures) ID and CVSS (Common Vulnerability Scoring System) score, start coordination with CERT@VDE
2023-04-27 – WAGO PSIRT shares draft advisory with us and CERT@VDE
2023-05-15 – CERT@VDE releases WAGO advisory
2023-05-17 – CERTAINITY & ONEKEY releases its advisory
